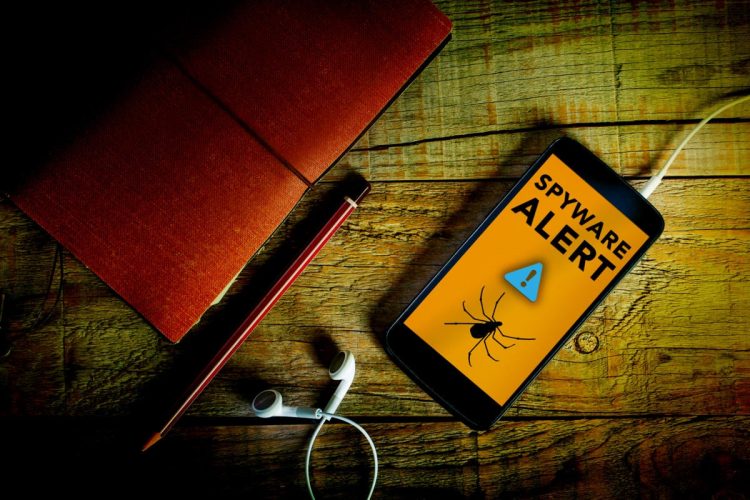
Google’s Menace Evaluation Group (TAG) has recognized Italian vendor RCS Lab as a spyware offender, growing instruments which can be getting used to take advantage of zero-day vulnerabilities to impact assaults on iOS and Android cellular customers in Italy and Kazakhstan.
In keeping with a Google blog post on Thursday, RCS Lab makes use of a mixture of ways, together with atypical drive-by downloads, as preliminary an infection vectors. The corporate has developed instruments to spy on the personal information of the focused units, the submit mentioned.
Milan-based RCS Lab claims to have associates in France and Spain, and on its web site lists European authorities businesses as shoppers. It claims to ship “cutting-edge technical options” within the area of lawful interception.
The corporate was unavailable for remark and didn’t reply to e-mail queries. In a press release to Reuters, RCS Lab mentioned, “RCS Lab personnel usually are not uncovered, nor take part in any actions performed by the related prospects.”
On its web site, the agency advertises that it gives “full lawful interception providers, with greater than 10,000 intercepted targets dealt with each day in Europe alone.”
Google’s TAG, on its half, mentioned it has noticed spy ware campaigns utilizing capabilities it attributes to RCS Lab. The campaigns originate with a novel hyperlink despatched to the goal, which, when clicked, makes an attempt to get the consumer to obtain and set up a malicious software on both Android or iOS units.
This seems to be achieved, in some instances, by working with the goal gadget’s ISP to disable cellular information connectivity, Google mentioned. Subsequently, the consumer receives an software obtain hyperlink by way of SMS, ostensibly for recovering information connectivity.
Because of this, many of the functions masquerade as cellular provider functions. When ISP involvement shouldn’t be doable, functions masquerade as messaging apps.
Licensed drive-by downloads
Outlined as downloads that customers authorize with out understanding the results, the “licensed drive by” method has been a recurrent technique used to contaminate each iOS and Android units, Google mentioned.
The RCS iOS drive-by follows Apple directions for distributing proprietary in-house apps to Apple units, Google mentioned. It makes use of ITMS (IT administration suite) protocols and indicators payload-bearing functions with a certificates from 3-1 Cell, an Italy-based firm enrolled within the Apple Developer Enterprise program.
The iOS payload is damaged into a number of elements, leveraging 4 publicly identified exploits—LightSpeed, SockPuppet, TimeWaste, Avecesare—and two just lately recognized exploits, internally generally known as Clicked2 and Clicked 3.
The Android drive-by depends on customers enabling set up of an software that disguises itself as a authentic app that shows an official Samsung icon.
To guard its customers, Google has applied adjustments in Google Play Defend and disabled Firebase initiatives used as C2—the command and management methods used for communications with affected units. Moreover, Google has listed a number of indicators of compromise (IOC) in its weblog submit, to assist safety professionals detect intrusions.
Copyright © 2022 IDG Communications, Inc.
Supply by www.computerworld.com